SQL Injection via XSS attack
Por um escritor misterioso
Descrição

Exploiting SQL Injection: a Hands-on Example

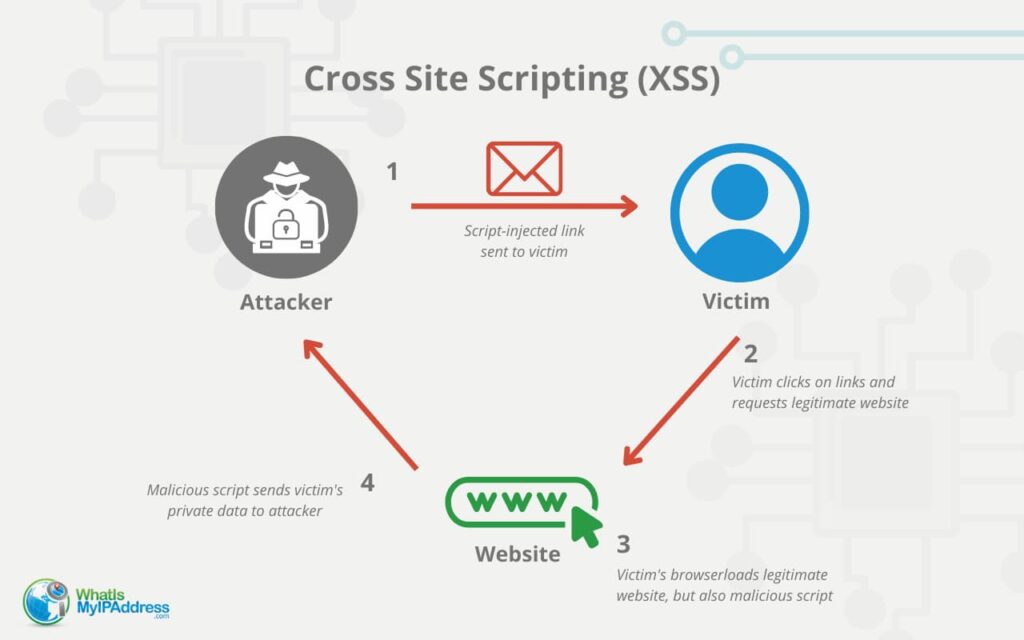
Difference Between XSS and SQL Injection

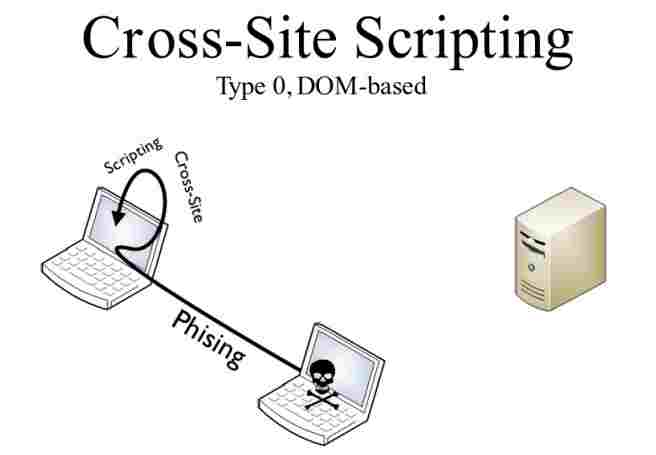
Syntax-based SQL/XSS injection detection
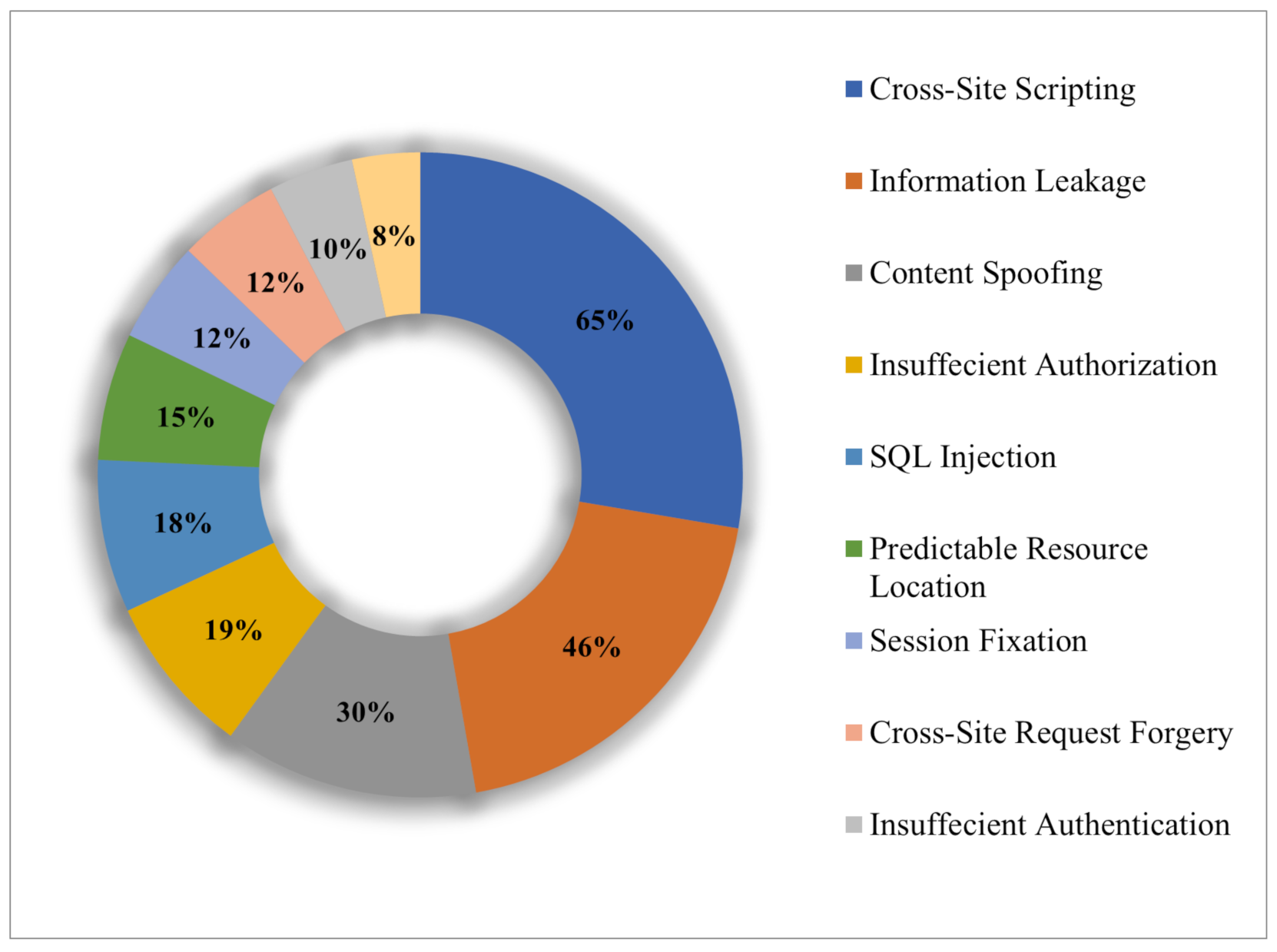
Electronics, Free Full-Text
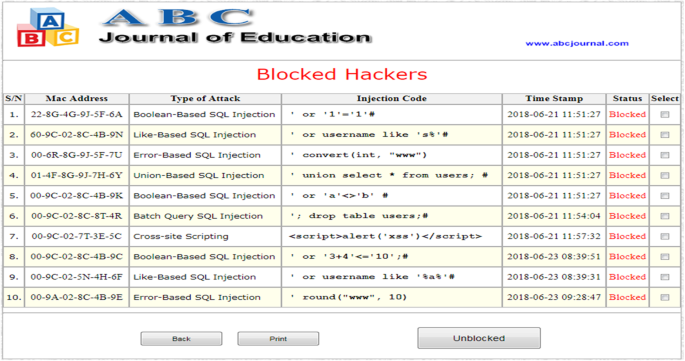
A novel technique to prevent SQL injection and cross-site
Defending Node Applications from SQL Injection, XSS, & CSRF

SQL Injection via XSS attack

Table I from Cross Site Scripting: Detection Approaches in Web
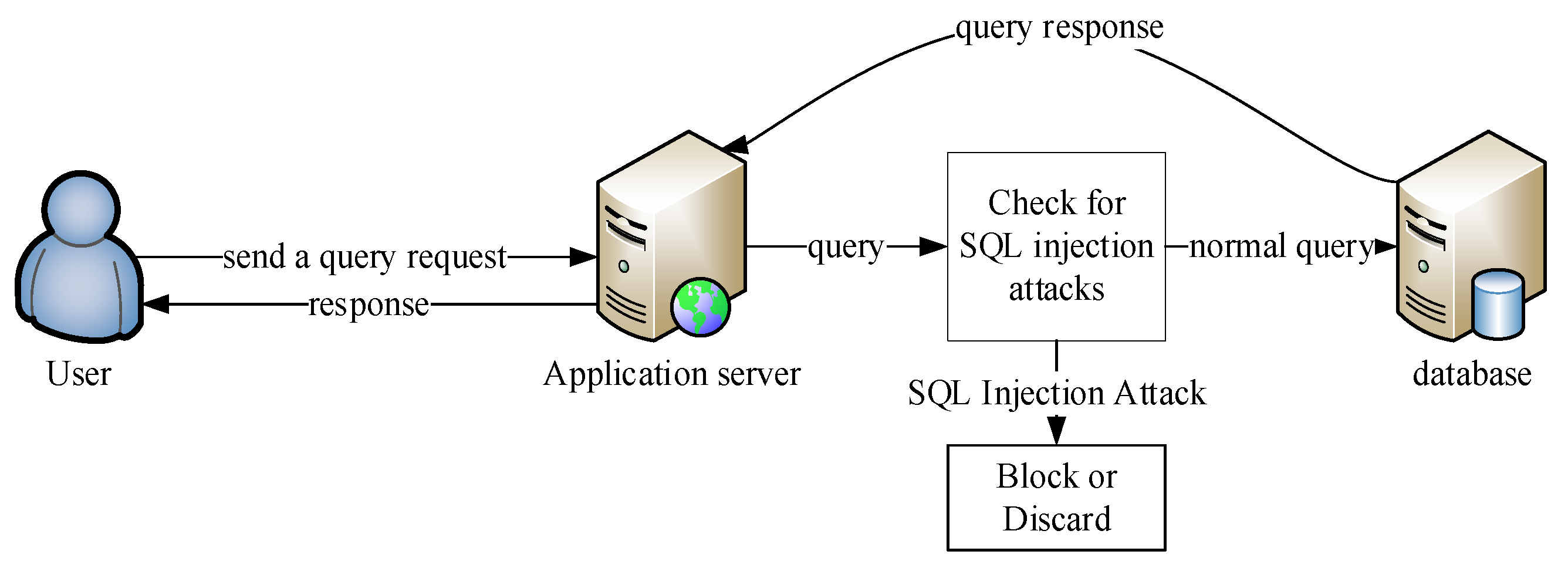
Electronics, Free Full-Text
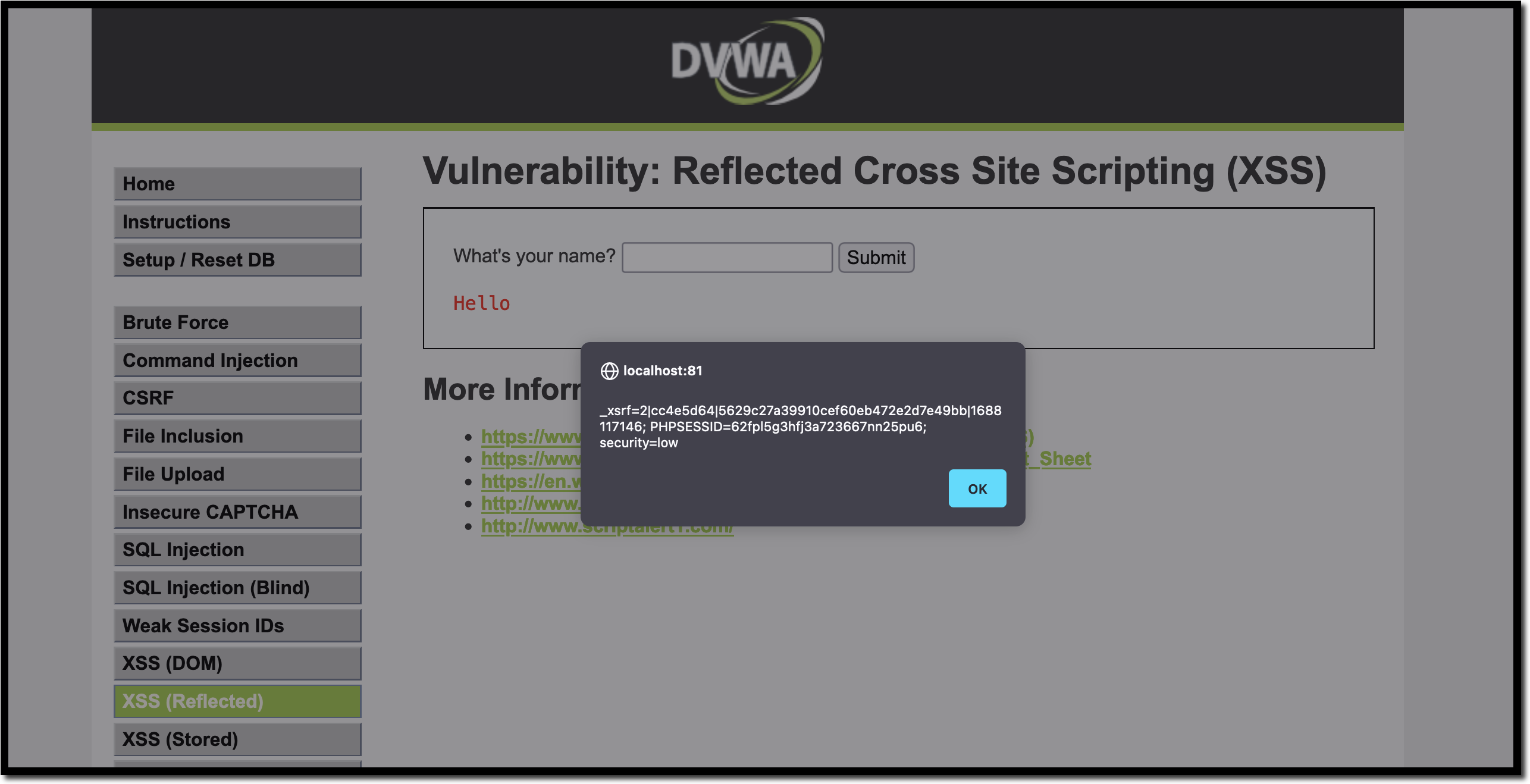
10 Practical scenarios for XSS attacks

Example of a SQL Injection Attack
de
por adulto (o preço varia de acordo com o tamanho do grupo)