Hackers Spotted Using Morse Code in Phishing Attacks to Evade
Por um escritor misterioso
Descrição
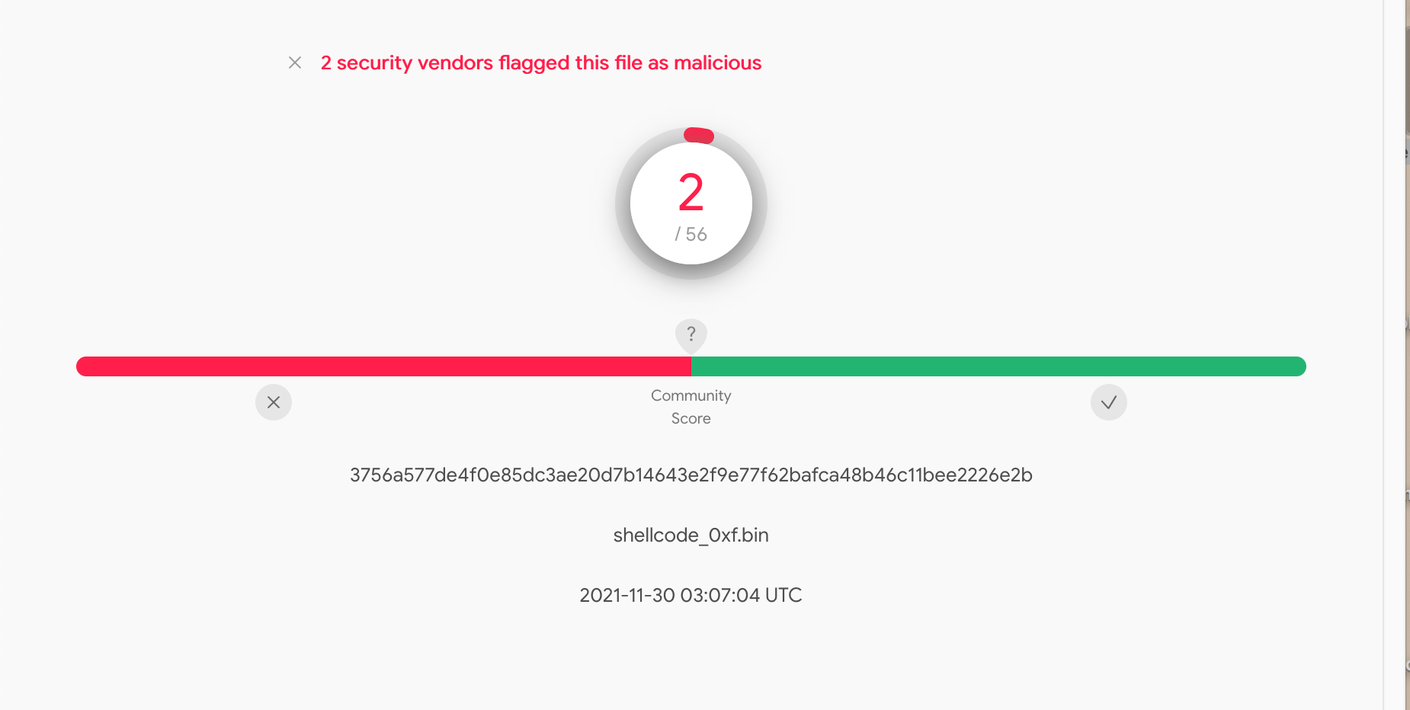
Hackers No Hashing: Randomizing API Hashes to Evade Cobalt Strike Shellcode Detection

CS4FN Advent 2023 – Day 18: cracker or hacker? Cyber security – cs4fn

one common technique - FasterCapital

Hackers Spotted Using Morse Code in Phishing Attacks to Evade Detection : r/ hacking

The Mirai Confessions: Three Young Hackers Who Built a Web-Killing Monster Finally Tell Their Story

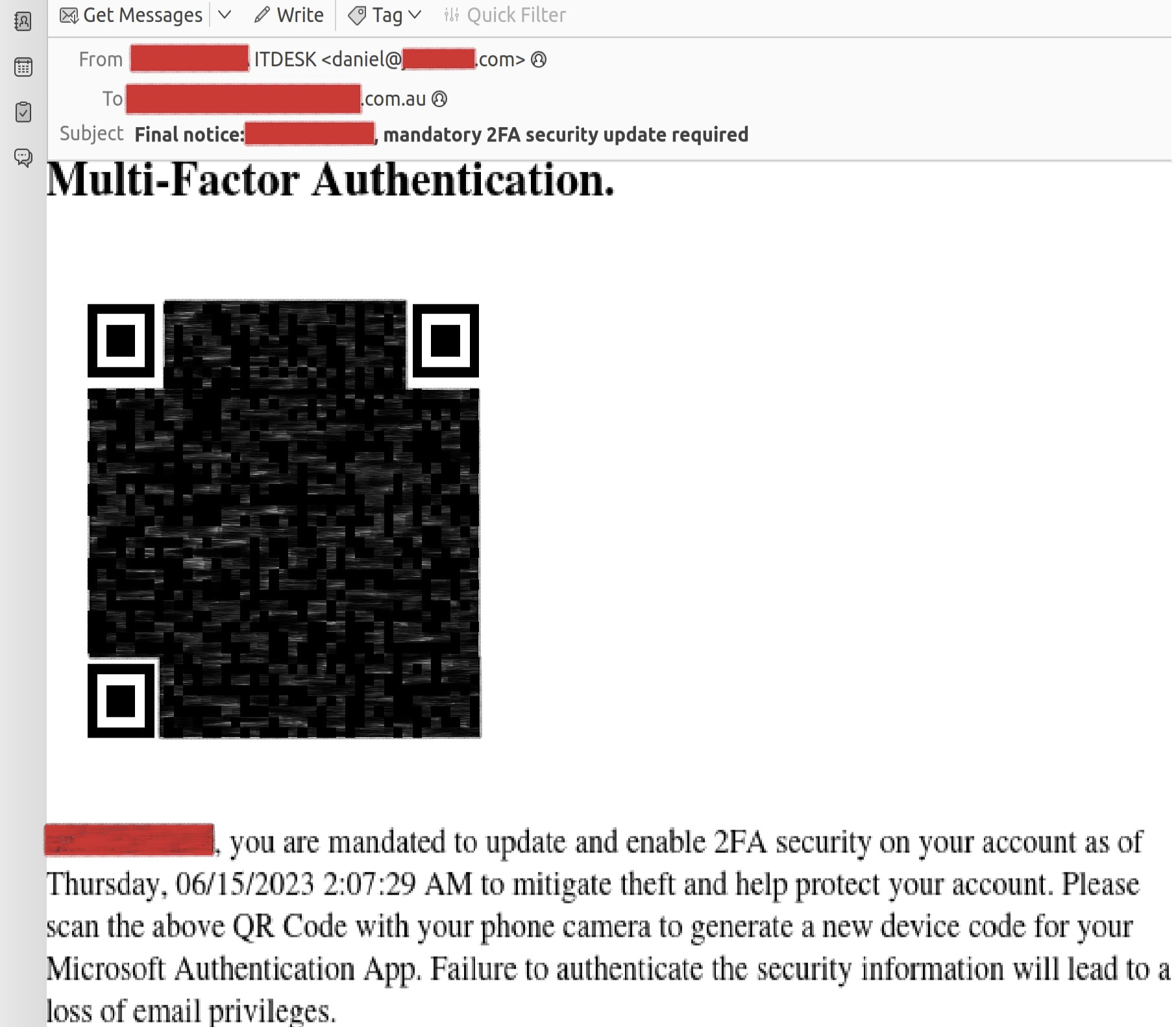
Phishing Email Attack Botched By The Hackers - Evgen Verzun Cybersecurity Blog

Secjuice Squeeze 55
%20(1).jpg)
Telefonica Tech · Blog · Telefónica Tech

Attackers use Morse code, other encryption methods in evasive phishing campaign
de
por adulto (o preço varia de acordo com o tamanho do grupo)